Is your organization prepared to respond to a cybersecurity incident? Are you on top of emerging cybersecurity threats? How well do you assess the effectiveness of your Cyber protection measures against potential threats?
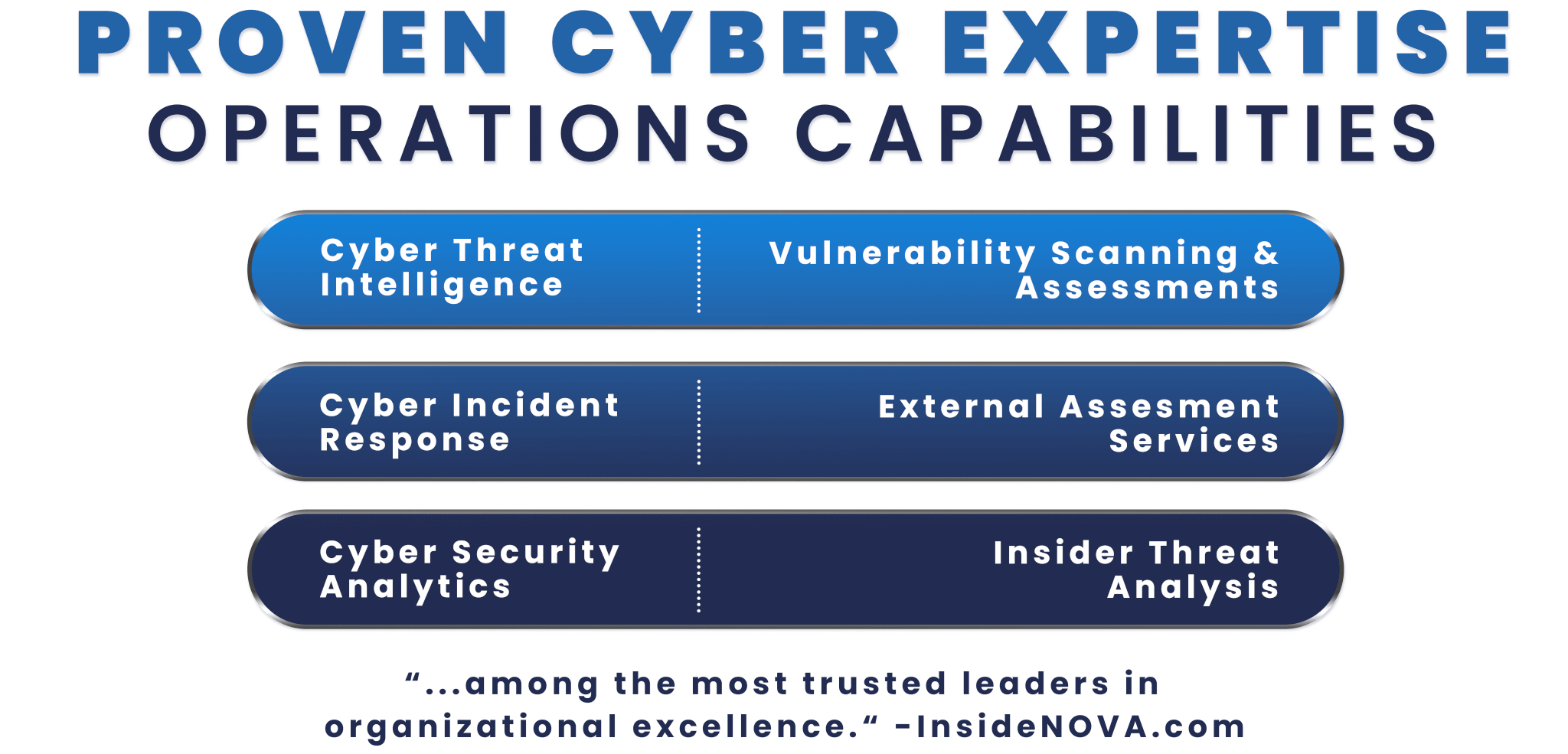
Our experts can help you assess the cyber readiness of your most mission critical systems.
HigherEchelon can improve your organizations cybersecurity posture by conducting penetration testing. Our experts mimic real-world attacks to identify vulnerabilities that could allow attackers to circumvent the security of an application, system, or network.
Our experts can help you prepare for a cyber incident, rehearse your plans, and be by your side if the worst occurs.
HigherEchelon experts can help you understand your environment, identify the scope of your security efforts, the systems and assets you want to protect. Using our expertise with frameworks such as NIST, we help you assess your current practices, identify gaps between those practices and best practices, and the implement, test and validate improvements, and implement continuous monitoring.
Our cyber experts take a proactive approach to understanding the threats your network faces by using network and behaviors and activities to find potential threats missed by traditional reactive methods.
Understand the real risks and vulnerabilities of your network through the lens of a threat model. Identify risks and prioritize them using a formal cost / benefit model.
Applying statistical tools, data mining and machine learning to a myriad of data sources such as aggregated network and system logs, network events, threat models and user behavior, our experts will help you identify patterns and make predictions.
Our experts provide a full spectrum of cyber support, including layer 3 and 7 firewall, IDS/IPS configuration and monitoring, log aggregation and analysis at scale, SIEM implementation and operation, and cyber forensics and malware analysis.
The VA-CSOC is responsible for identifying indicators of adversarial presence on the VA network on a 24/7/365 basis via maintaining an understanding of the motivations, tactics, techniques, and procedures of cyber adversaries. If a loss of confidentiality, integrity, or availability has occurred we move to disrupt the adversary’s activities through containment, mitigation, and eradication. The VA-CSOC performs independent verification and validation of VA’s cyber security posture, performs cyber-related reporting to outside Agencies, and leads Departmental efforts to prepare for and defend against emerging and imminent threats.